A SOC Analyst who
|
beyond the noise…
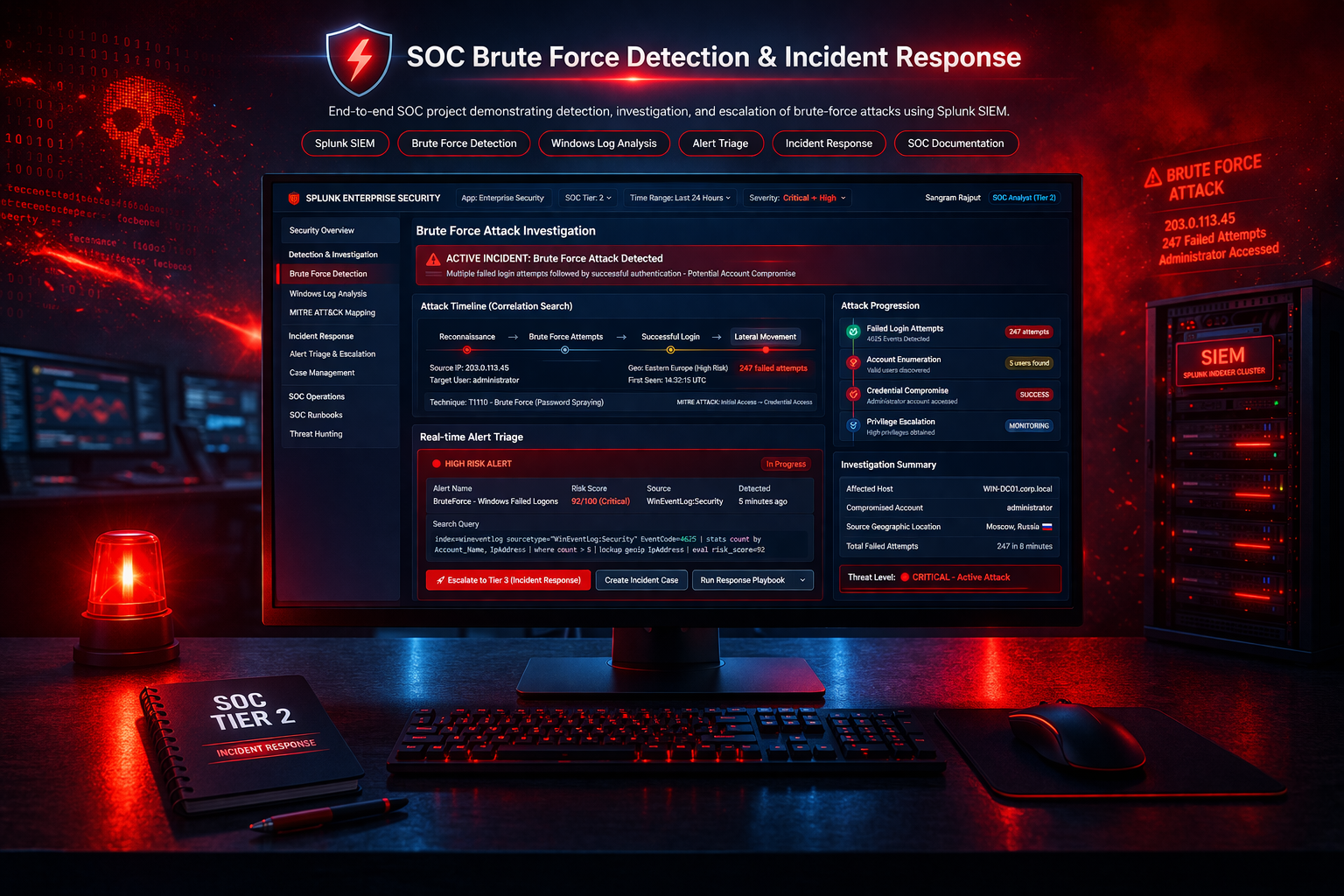
Focused on alert correlation, incident investigation,
and real-world SOC response using Splunk SIEM.